LET'S TALK GEMINI!
key features
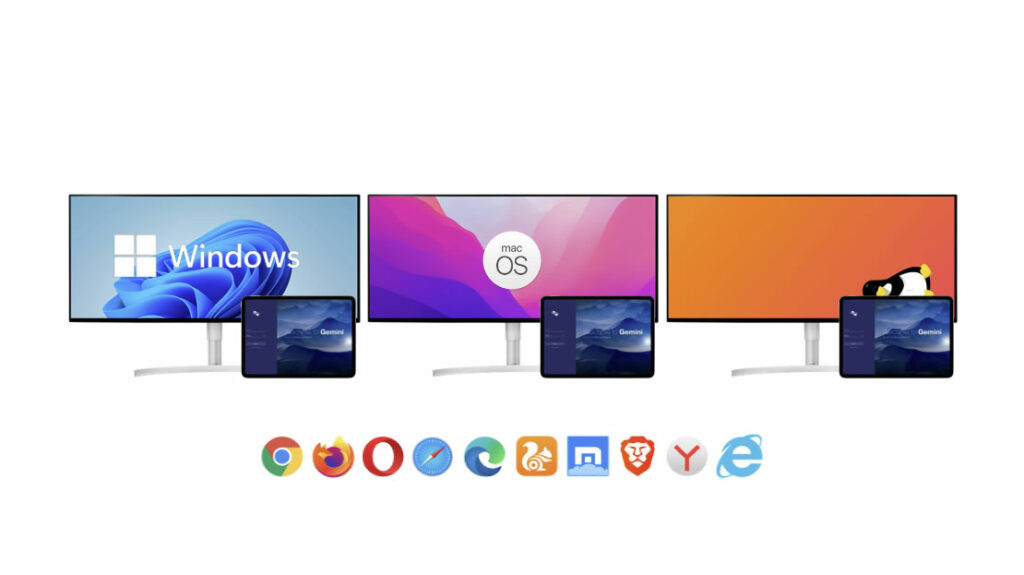
As you like
Use GEMINI on the device you prefer – iPad, Android tablet, notebook or desktop, and in your favorite web browser.
Cloud
On-premises
Hybrid operations
ANYTIME ANYWHERE ANYONE

Open System
This is not about open source technologies. It is about openness in adopting requirements. It is about openness in integrating with third-party media processing devices, third-party systems and appliances. Media operations are quite complex and to build a real solution that addresses the needs of today and the future does not require nor should it rely on an isolated system. It means integrating with the outside world. The openness of GEMINI scores high here.
AI-enriched metadata
AI is heavily utilized in GEMINI to enrich the descriptive metadata. GEMINI integrates with third-party AI systems to generate timeline annotations (description of segments, speech–to-text transcription, face and object recognition, all linked to particular markers in the asset timeline). But that’s not all, AI helps GEMINI to optimize search results and deliver them faster to you.
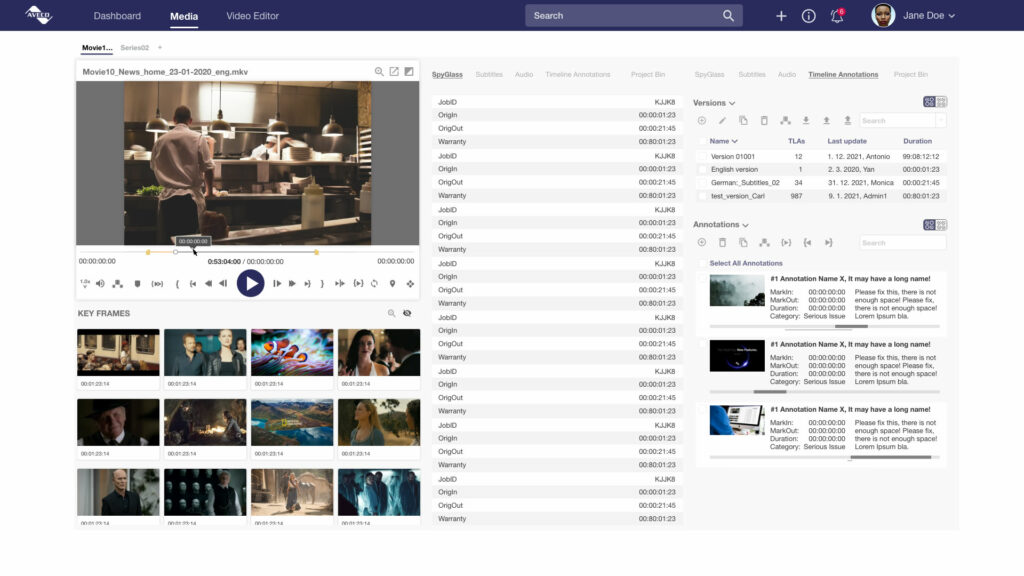
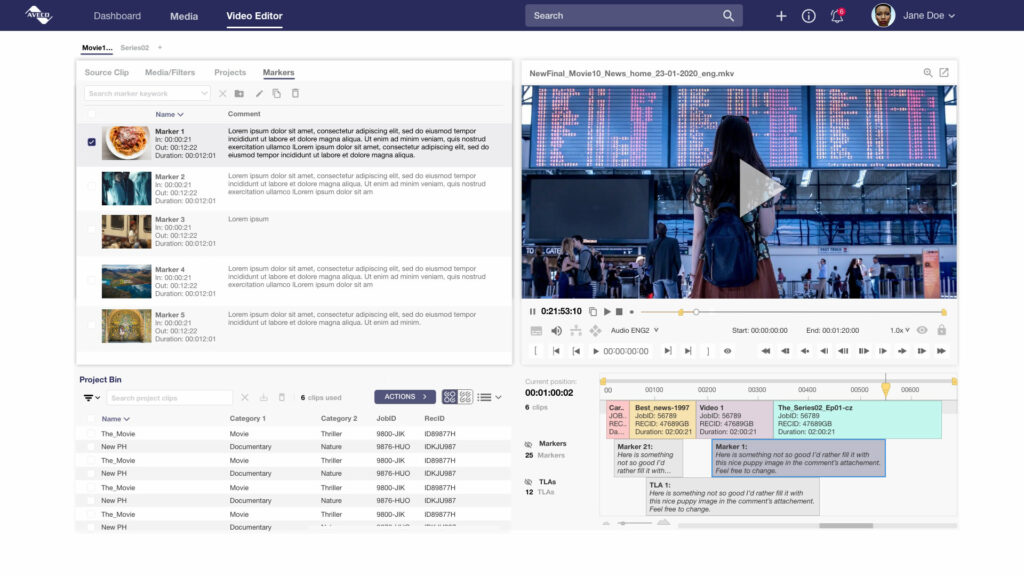
Timeline Annotations
OK, we have the metadata structure to describe the whole asset. But, every frame of that asset brings something different, something interesting. Timeline annotations are here to describe particular frames or particular segments inside the asset. Each clip can have multiple sets of timeline annotations, such as movie segmentation for playout, speech-to-text transcription, subtitles or markers for soccer goals. New types of timeline annotations can be defined and set up as required. The timeline annotations — whether created manually or imported — are full-text searchable and elevate the search success rate to another level.
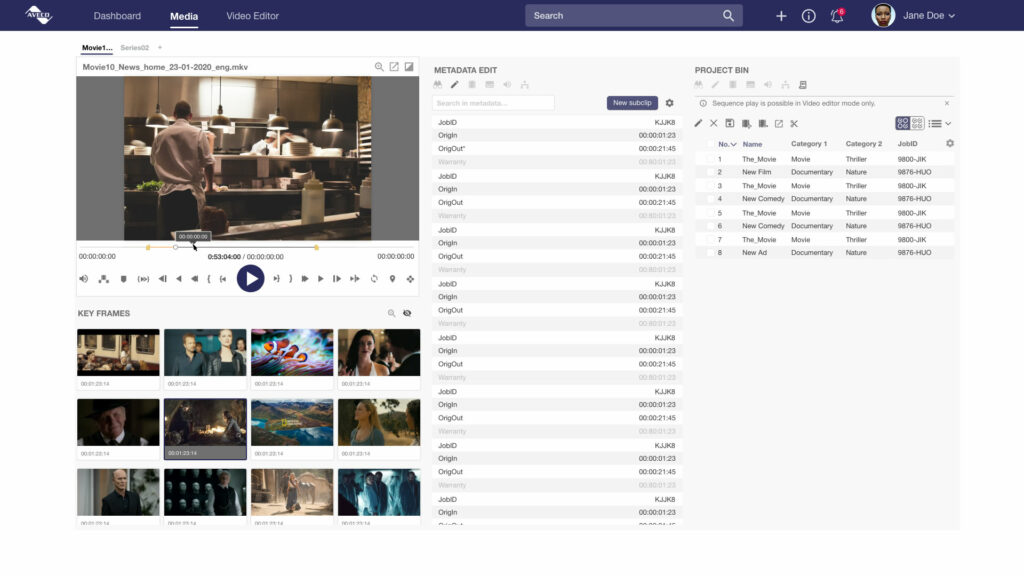
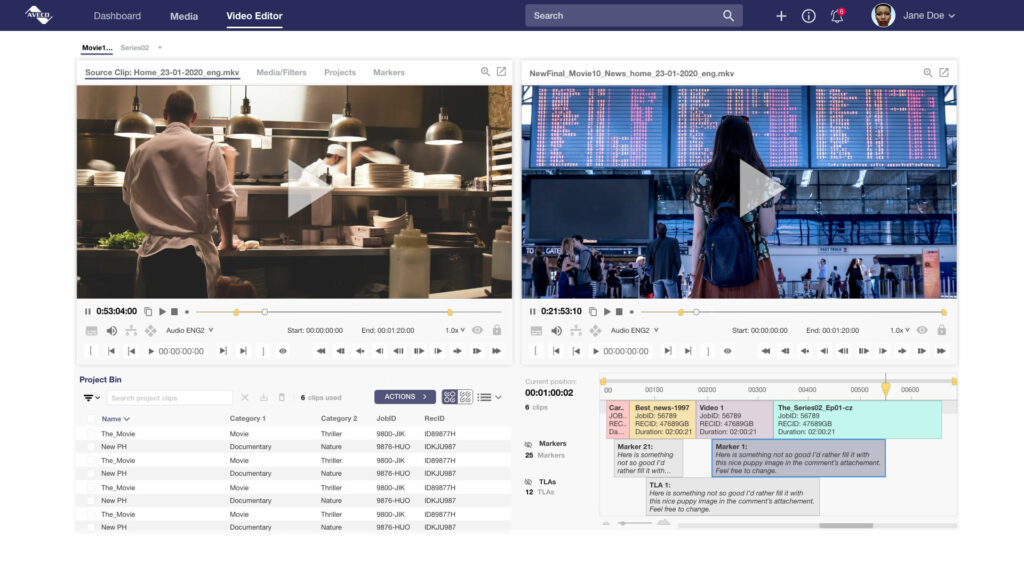
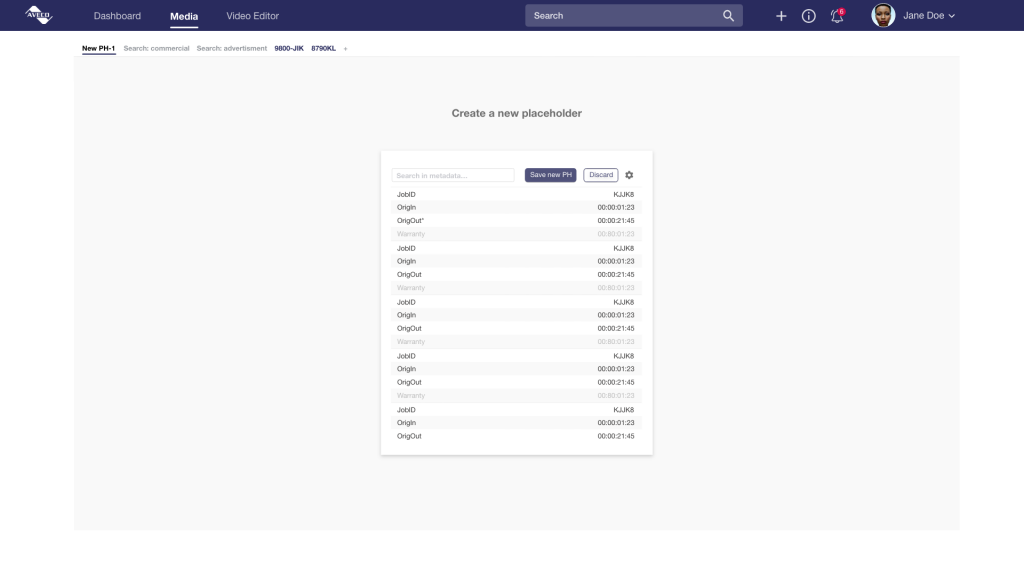
Video Editing
Multiple ways of browsing and editing assets are available by using the GEMINI web UI. The detail view of an asset includes a frame accurate low-res player for browsing and trimming. The Video Editor is a tool to create new assets by searching for source material, creating a timeline from selected media segments, and then passing the timeline to a back office renderer or to an NLE for craft editing. And, users can drag-and-drop a clip from the GEMINI plugin straight to the NLE bin or timeline.

Scheduling and Distribution
All leading Newsroom Computer Systems have been integrated with GEMINI to deliver the perfect news workflow. There are placeholders, low-res and hi-res video editing, as well as our news production automation tools to produce live news bulletins, ingest them automatically and pass the ingested assets back to GEMINI for further processing. GEMINI can integrate with Traffic Management Systems for ingest requests, status and metadata exchange and provision of scheduled media for playout or web publication. Likewise, GEMINI can provide media to WAN transfer systems for media delivery to partners or business customers as well as integrate with web CMS or streaming platforms for online publication.
Playout and News Production
The Manage from the media paradigm mentioned above assures efficiency. But… it’s the Deliver that brings revenues. — robust, redundant, field proven, with unified experience and fast turnaround. Efficiency squared.
Collaboration
In GEMINI every asset is a www link. Share the link with your teammates via e-mail or your preferred instant messaging platform. Work together on projects, they are https link as well.
Architecture to scale
The architecture of GEMINI utilizes microservices, Dockers, Kubernetes and other modern and proven technologies. The ability to run in the cloud as well as using on-premises COTS devices allows us to deliver the right-fit solution for any organization and workflow, and then scale GEMINI as requirements evolve. From thousands to millions of media production automation, each story can be ingested individually and handed over to GEMINI for further processing and/or online publishing. Our ISO ingest solution is linked to GEMINI, too. Any way the assets arrive, the relevant workflows apply. GEMINI always knows what to do.

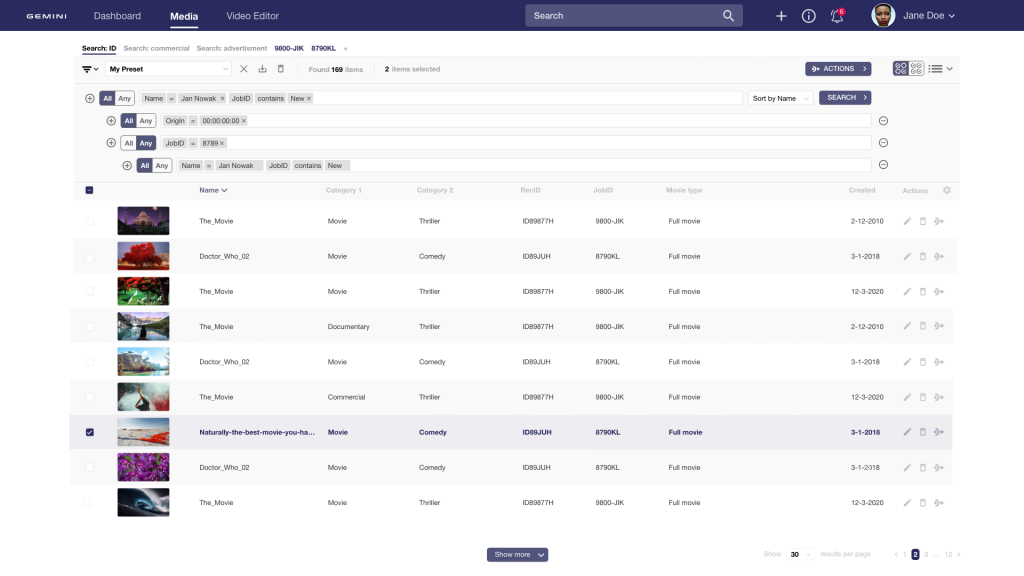
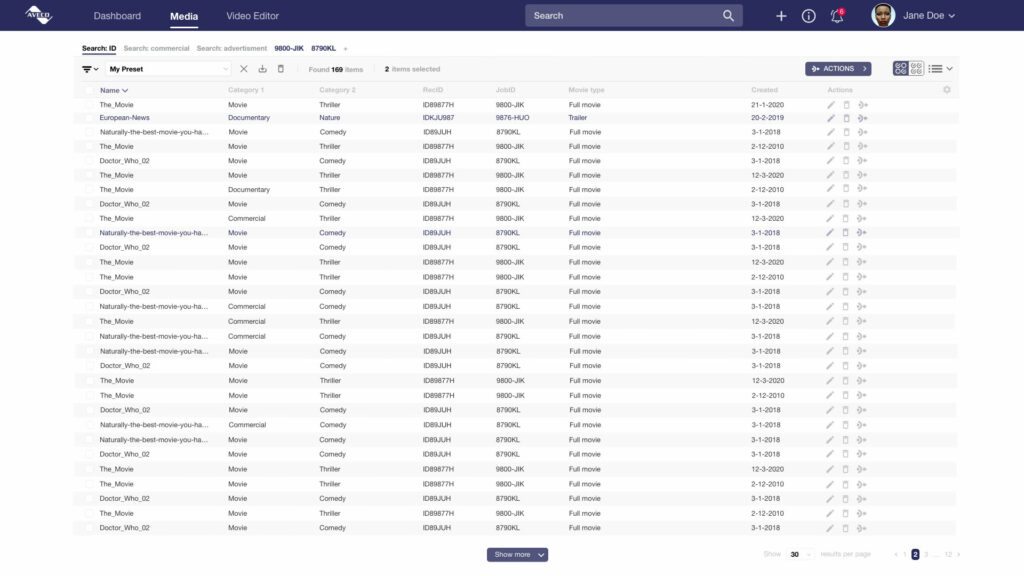
Search
Users can utilize complex filtering, targeted search as well as full-text search. Queries can be saved to simplify repetitive jobs. The found media can be browsed, edited, exported or processed by a chosen workflow.
Media Processing
The lifecycle of an asset describes how to take the incoming material and create a final product from it. The related workflows involve a great deal of media processing, such as transcoding, audio manipulations, QC, segmenting or stitching. There may be GEMINI is able to deliver assets to various targets in the specific media and metadata formats required. Yet, there is one aspect that is globally outstanding: Our product range. GEMINI MAM together with ASTRA MCR playout solution and ASTRA Studio news production automation represent the best integration of MAM and automation in the world — because there is no integration. The microservices of these products talk directly to each other, all using the same database. It’s an elegant solution assets, from tens to hundreds of users, from out-of-the-box workflows to the most complex operations involving third-party media appliances, GEMINI can meet today’s requirements and then expand as you grow.


Storage and archive
GEMINI manages all storage devices in the facility, including NAS and SAN systems, ingest and playout videoservers, cloud-based storage, as well as LTO archive and non-spinning disk archive. GEMINI handles the media transfers between them, taking care of any necessary file processing and automatic delivery of related objects and data. GEMINI, in cooperation with Aveco automation products, provides the best possible Hierarchical Storage Management, as the automation systems know exactly when and where each asset is required and when it is planned to go to air. This helps to optimize storage utilization.
Assets coming in
GEMINI helps you ingest assets in many ways. There is manual and scheduled baseband ingest. There is an automatic file ingest linked to watchfolders as well as manual upload. GEMINI integrates with third-party media exchange solutions. And more — our playout automation solution automatically ingests every live event and passes it on to GEMINI. With our studio/news various appliances involved in the process, including Aveco’s as well as third-party products, orchestrated by GEMINI. Workflows are fully automated except for tasks such as audio mixing or color correction — where the artistic control of a person is paramount. Those tasks are assigned to task lists for the relevant user roles.
Metadata
Rich metadata structure helps to describe every aspect of an asset. The structure can be further enhanced to adopt to the specific needs of a user. Metadata comes from various sources. Technical metadata are read from the asset. Descriptive metadata can be generated, imported from external data sources or just a XML file, as well as edited manually.
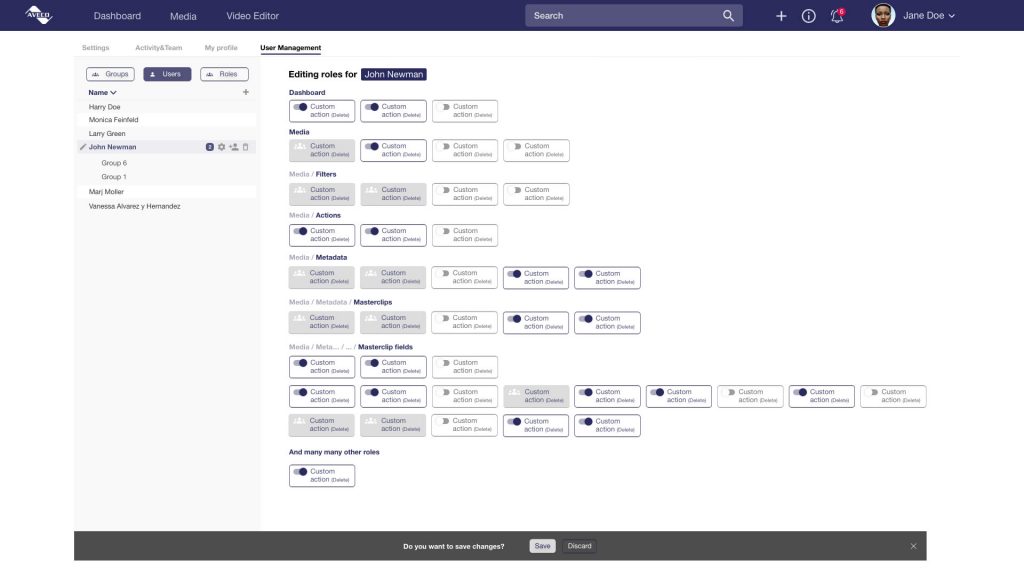
User Management
Defining roles of users is an important part of every organization. Once defined, workflows can be unleashed and run smoothly. User rights in GEMINI define access to tools and assets, as well as to individual metadata fields.